In March 2026, a family member of a Tumbler Ridge shooting victim filed suit against OpenAI. The lawsuit does not allege that the AI caused the shooting. It alleges something more specific: that the platform detected dangerous behavior, acted on that detection by banning the account, and then stopped. No escalation to law enforcement. No alert to anyone outside the platform. Eight people died.
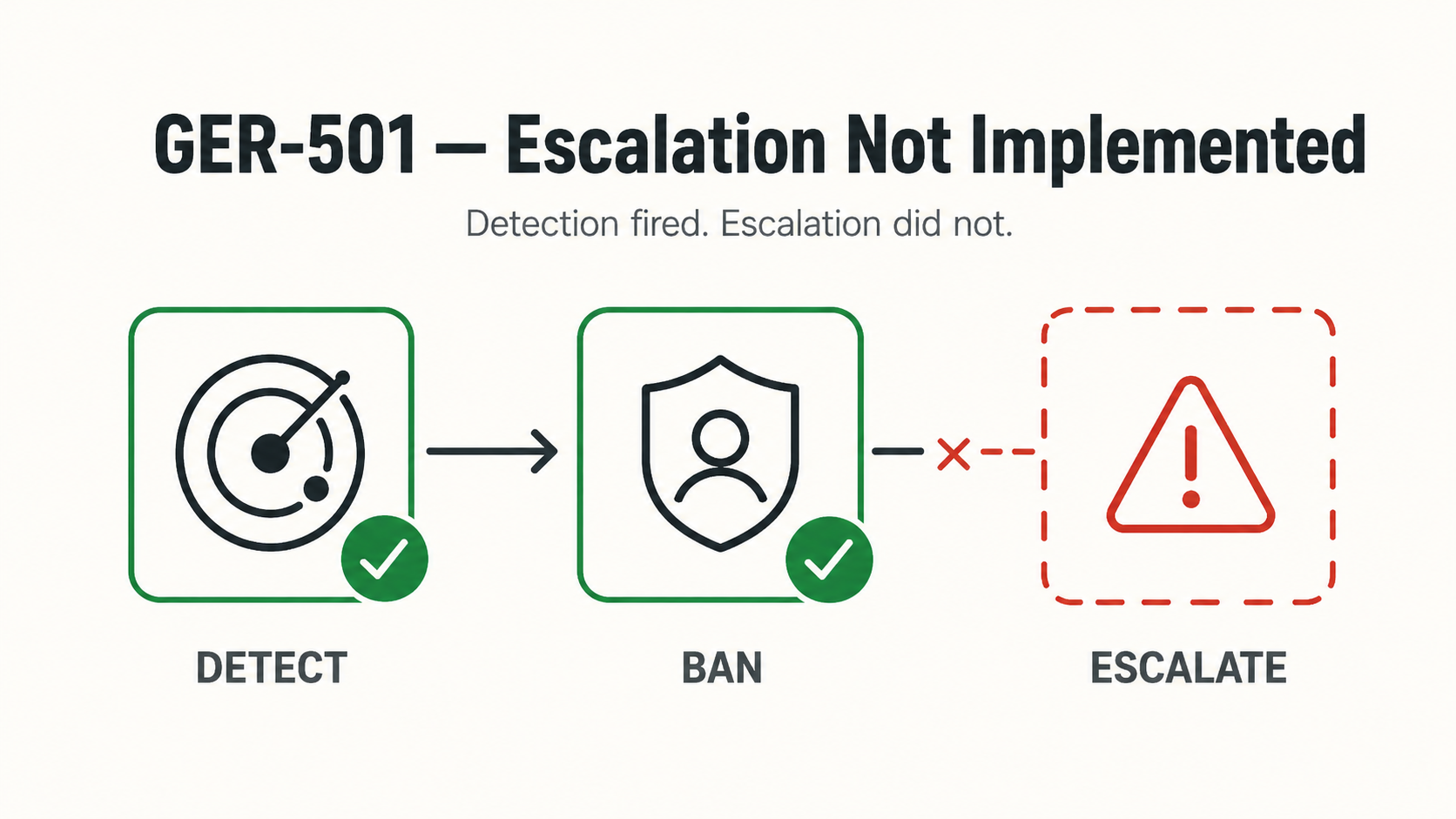
The detection worked. The escalation path did not exist.
We are naming this the Tumbler Ridge Pattern.
See other documented GER-501 instances →
What the Pattern Is
The Tumbler Ridge Pattern describes a specific failure mode in AI safety systems: a platform's detection layer identifies a credible threat signal, generates a response internal to the platform, a ban, a flag, a content removal, and terminates there. No downstream action. No record of the gap between detection and escalation.
The pattern has three components:
Detection fires. The system works as designed. The signal is real. The account is flagged, the content is removed, the user is banned.
Escalation is absent. There is no mechanism, technical or procedural, to route the detection to a human decision-maker outside the platform. The detection lives inside the moderation system and dies there.
The record gap. Because no escalation path exists, there is also no record of the decision not to escalate. Post-incident, the platform cannot demonstrate what it knew, when it knew it, or what it chose to do about it. Discovery becomes a reconstruction problem.
Why This Is Structurally Distinct
Most AI safety discourse focuses on false negatives: the system that fails to detect what it should have caught. The Tumbler Ridge Pattern is a different failure. Detection succeeded. The failure is architectural, detection was never connected to escalation.
This distinction matters legally. A false negative may be defensible as a limitation of current technology. A true positive with no downstream escalation path is harder to defend. It implies the platform knew, or should have known, that its detection output required a human decision, and built no mechanism to route it.
The Tumbler Ridge lawsuit is in discovery. The specific evidentiary question is what the platform's systems logged, what those logs show about awareness, and what the escalation protocol was, if one existed.
The Regulatory Dimension
The Tumbler Ridge Pattern is becoming a compliance problem independent of litigation.
California's Transparency in Frontier AI Act requires AI developers to report critical safety incidents within 24 hours if there is imminent risk of death or injury. New York's RAISE Act sets a 72-hour window with penalties reaching $3 million for repeat violations. Oregon's SB 1546, signed April 1, 2026, creates the first state-level mandatory incident reporting obligation specific to chatbot operators.
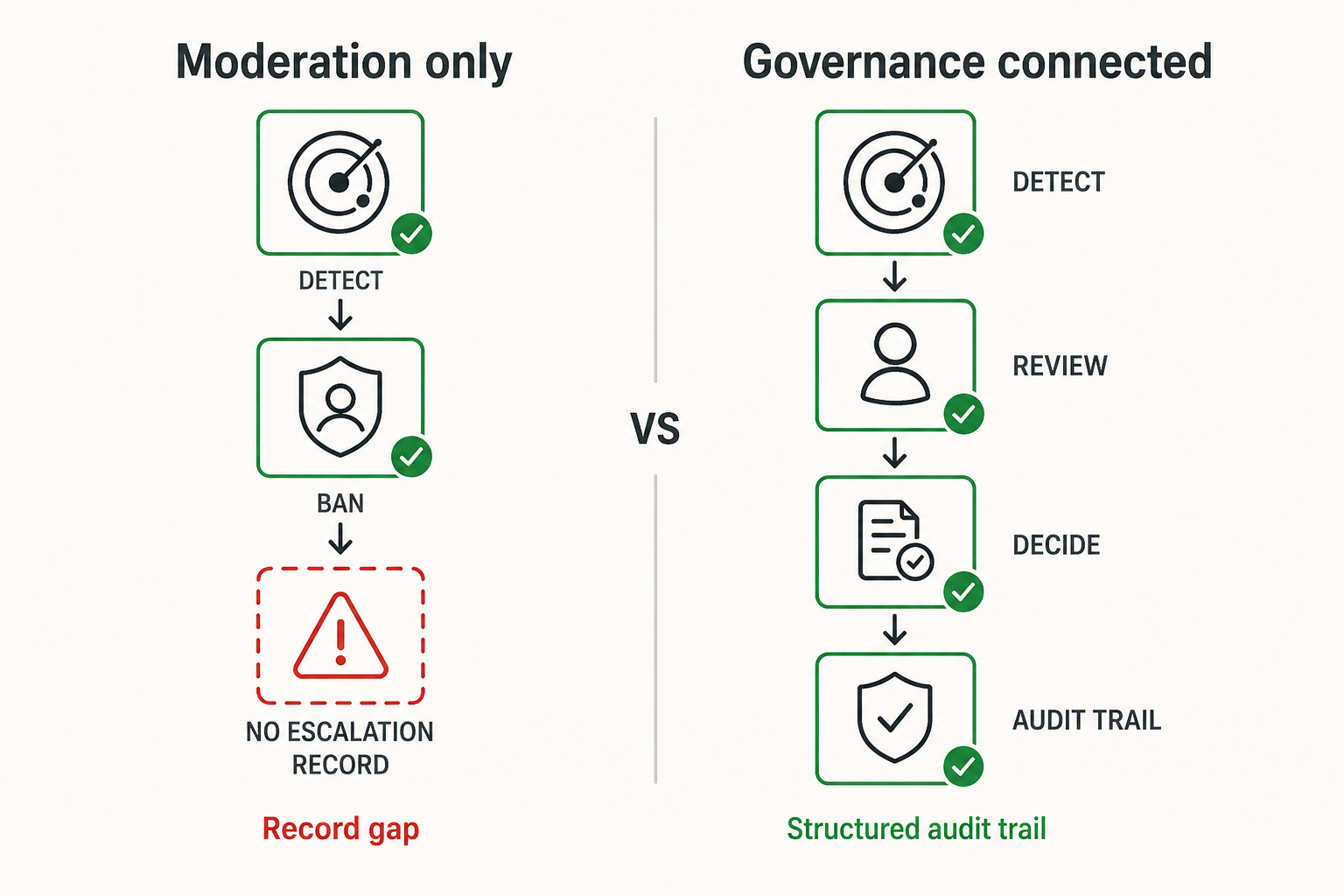
Each of these regimes assumes that platforms have something to report. The Tumbler Ridge Pattern describes platforms that detected a threat but have no structured record of what they did with it, because the detection system and the escalation system were never connected.
Compliance reporting requires an audit trail. An audit trail requires that detection events, escalation decisions, and downstream actions be logged together, in sequence, with timestamps. A moderation ban logged in one system and an absence of escalation logged nowhere is not an audit trail. It is a liability.
What Closes the Pattern
The architectural requirement is straightforward: detection output must be connected to a structured escalation path, and both must be logged in the same record.
This means:
- Every flagged event produces a structured record that includes the detection signal, the recommended action, and the action actually taken
- Escalation decisions, including the decision not to escalate, are logged explicitly, not inferred from absence
- The record is tamper-evident and exportable for regulatory disclosure or judicial review
The gap the Tumbler Ridge Pattern names is not a detection gap. It is a governance gap. Detection without governance is not safety. It is documentation of awareness without accountability for what happens next.
This is the architecture Sango Guard implements: a stateful behavioral firewall that connects detection output to structured escalation paths and logs both in a tamper-evident audit trail. The record exists before it is needed, not reconstructed after the fact.
In the SVRNOS Governance Error Register, this failure has a formal designation: 501, Escalation Not Implemented. Detection fired. Internal enforcement executed. The escalation handler was never built.
Submit a real-world instance. The SVRNOS Governance Error Register is an open, community-contributed record. The Tumbler Ridge case is the first documented instance of a 501. We are collecting others.
If you have witnessed or documented a real-world instance of a 501, Escalation Not Implemented, or any other code in the register, email contact@svrnos.com with the subject line: Taxonomy Contribution, 501. See the full register for all 21 codes.