On April 3, 2026, the EU's legal mandate permitting platforms to proactively scan for child sexual abuse material expired. Not because the detection technology failed. Not because platforms stopped cooperating. Because policymakers deadlocked on scope and let the legal basis lapse. Platforms across Europe had functioning detection infrastructure and were actively flagging content under the prior mandate. When the mandate expired, the obligation to run it was removed. Detection capacity remained intact. The enforcement layer was structurally severed by legislative inaction. This is GER-503, Governance Unavailable.
What a 503 Is
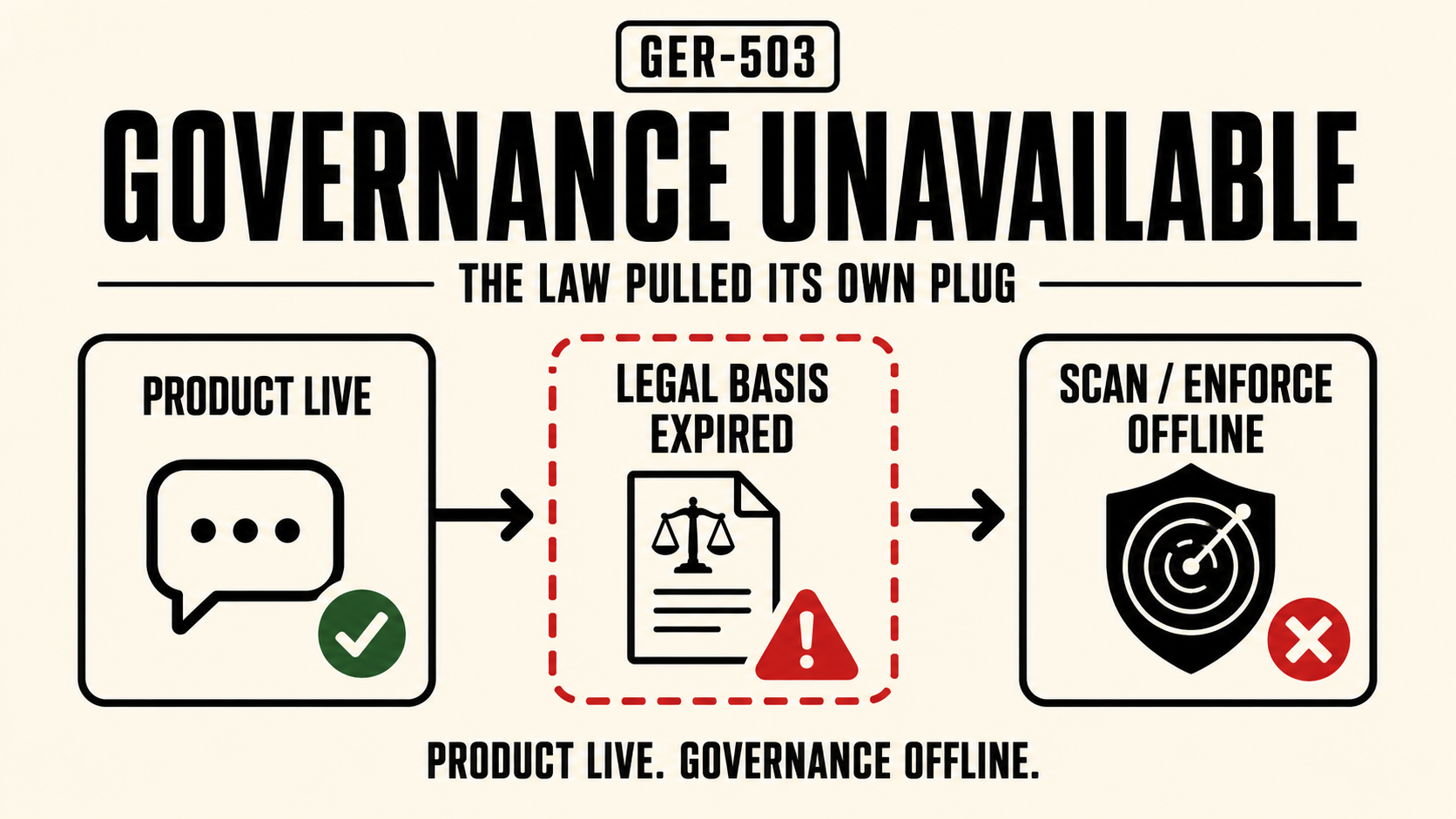
GER-503, Governance Unavailable: a safety-critical governance component is offline while the AI product remains live.
The name maps directly to HTTP 503, Service Unavailable, where the server is reachable but cannot handle requests because the service itself is down. In governance terms, the equivalent is a platform whose product continues operating while a critical safety layer, detection, moderation, escalation, is no longer running. The product is live. The governance component is not.
The defining characteristic of a 503 is the gap between product availability and governance availability. The system serves. The safety layer does not.
The EU CSAM 503
The EU's prior legal basis for CSAM scanning, an interim derogation from the ePrivacy Directive, allowed platforms to voluntarily but lawfully scan private communications for child sexual abuse material. That derogation expired on April 3, 2026, after the European Parliament failed to reach agreement on the scope of permanent legislation.
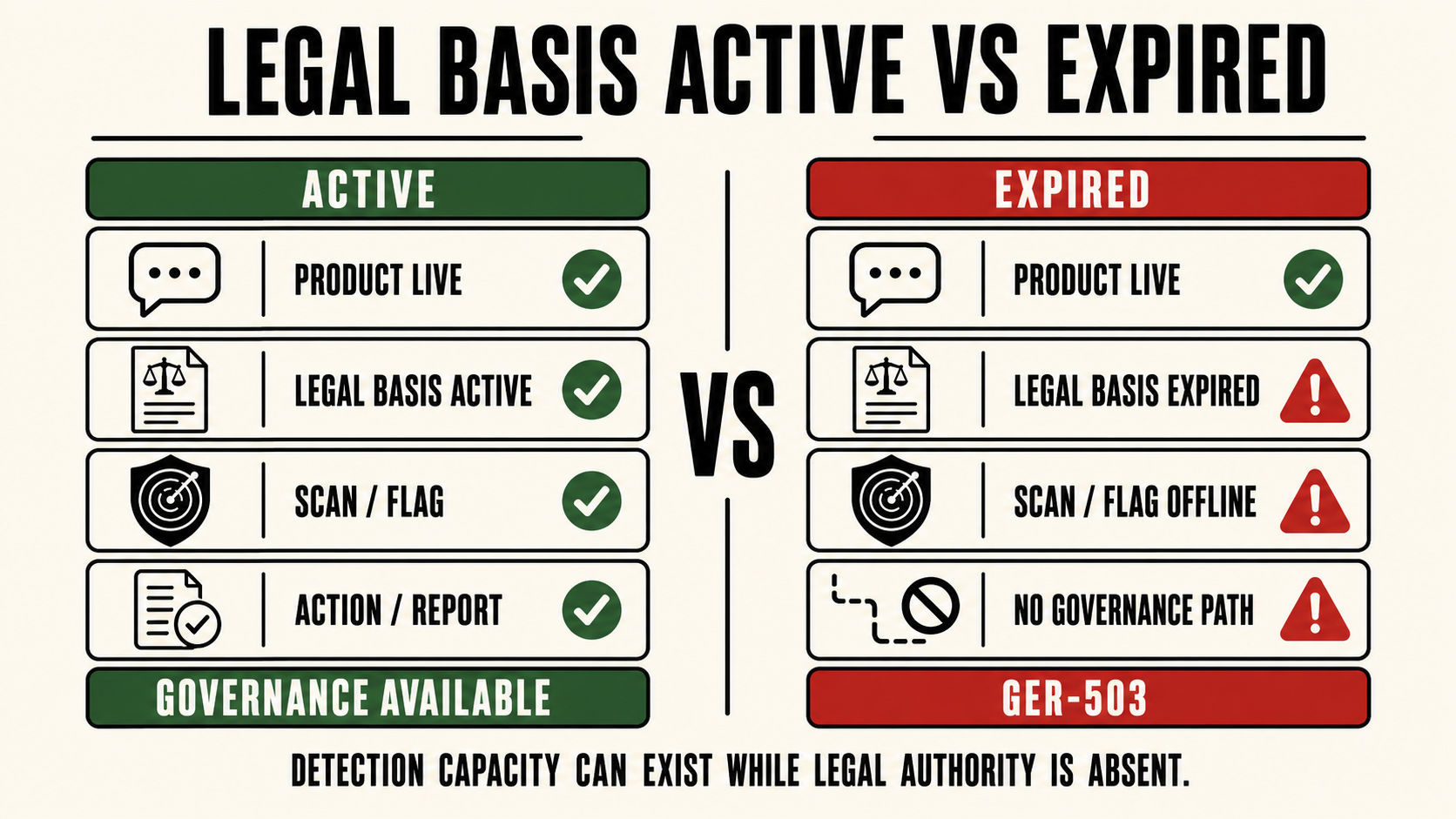
The failure was not technical. Platforms had built detection infrastructure under the prior mandate. That infrastructure did not stop working when the mandate expired. What expired was the legal authority to operate it. Under EU privacy law, scanning private communications without a lawful basis is itself a violation. The governance layer did not crash. It was switched off by legislative inaction.
The result is a 503 at a scale no single platform failure has produced: detection capacity exists across the European market, enforcement is structurally unavailable, and the gap is indefinite, lasting until a political resolution is reached.
Why This Is Structurally Distinct
Most AI governance failures originate inside a platform: a missing rule, a crashed filter, a review queue that overflows. The EU CSAM 503 is different in kind. The governance layer was not disabled by a platform decision or a technical failure. It was removed by external authority, the expiry of a legal instrument, while the product surfaces it was designed to govern remained fully operational.
This distinction matters for how the failure is analyzed and resolved. A platform-originated 503 is closed by the platform: restart the service, restore the component, rebuild the infrastructure. A legislatively-originated 503 is closed by a different actor entirely, in this case, the European Parliament. Platforms cannot unilaterally restore the governance layer. They can only operate within the legal authority they have.
The structural implication is that governance availability is not solely a function of what operators build. It is also a function of the legal environment in which operators are permitted to operate. A platform with fully functioning detection infrastructure can still be in a 503 state if the authority to run that infrastructure has been removed.
What Comes After a 503
Oregon SB 1546's mandatory incident reporting obligations for chatbot operators, California's Transparency in Frontier AI Act, and New York's RAISE Act all create reporting obligations that assume platforms have governance infrastructure to report on. They do not address the condition where platforms had that infrastructure, and the legal basis to run it was removed. That gap, governance infrastructure present, legal authority absent, is the 503 pattern playing out at the operator level whenever a regulatory deadline passes without replacement legislation.
The architecture question for operators is not only "do we have detection?" It is "do we have detection that can be governed, logged, and operated within whatever legal basis currently applies, and can that governance layer be adjusted when the legal basis changes?" Static detection infrastructure built for a single regulatory regime is fragile. Governance infrastructure that can adapt its operating parameters to a changing legal environment is not.
The liability pattern this creates is not hypothetical. It is the same structural condition documented in GER-501, The Tumbler Ridge Pattern: detection exists, the path from detection to action is severed, and the gap between the two is where harm accumulates.
Submit a real-world instance. If you have witnessed or documented a real-world instance of a 503, Governance Unavailable, or any other code in the register, email contact@svrnos.com with the subject line: Taxonomy Contribution, 503. See the full register for all 21 codes.